How AI Powers Real-Time Vulnerability Mapping
Real-time vulnerability mapping transforms how organizations manage security risks by providing continuous, up-to-date threat insights. Unlike periodic scans, it works 24/7 to identify vulnerabilities, prioritize risks, and support faster remediation. AI plays a key role by automating processes, reducing false positives, and cutting manual workloads. For example, Microsoft’s Vuln.AI reduced vulnerability insight time by 70% and halved triage time.
Key takeaways:
- AI improves prioritization: Only 1.6% of "High" or "Critical" vulnerabilities need immediate action, reducing manual effort by 98.4%.
- Faster response: AI speeds up remediation, reducing resolution time by up to 90%.
- Advanced technologies: Machine learning detects anomalies, NLP analyzes threat intelligence, and dynamic scoring ranks risks based on context.
Implementing AI requires integrating tools, enabling continuous monitoring, and automating mapping. While challenges like costs and model drift exist, a hybrid approach combining AI and human oversight ensures reliability. The future of AI in security lies in automating remediation and delivering clear, actionable insights for teams.
I’ve seen you get hacked! (AI Real-Time Attack Simulation) – Nithen
sbb-itb-9b7603c
AI Technologies That Enable Real-Time Vulnerability Mapping
Three key AI technologies are reshaping vulnerability mapping, turning it from a reactive task into a proactive security strategy. These technologies fill gaps left by manual processes, offering faster, smarter, and more context-aware solutions. Together, they enable continuous and proactive monitoring for vulnerabilities.
Machine Learning for Anomaly Detection
Machine learning models play a crucial role by establishing baselines for normal behavior using historical data from networks, applications, and endpoints. Once these baselines are set, the models continuously monitor for unusual activity – like unexpected logins, data transfers, or resource usage – that could signal an active threat. This approach catches issues that traditional signature-based tools might overlook, including new and previously unknown attack methods.
By learning from past outcomes, machine learning systems can filter out harmless anomalies, allowing security teams to focus on real threats. This real-time detection is scalable, offering visibility across thousands of assets, and is key to identifying potential risks as they emerge.
Natural Language Processing (NLP) for Threat Intelligence
Natural Language Processing (NLP) enables faster, more comprehensive analysis of unstructured threat intelligence from sources like blogs, vendor advisories, and CVE databases. Unlike manual methods that depend on structured feeds, NLP can spot vulnerabilities even before they’re officially documented. As noted by Diligent:
"AI uses natural language processing to identify emerging vulnerabilities from security blogs and vendor advisories before official CVE publication".
For example, the Security Bulldog uses its own NLP engine to process open-source cyber intelligence from platforms such as MITRE ATT&CK and CVE databases. This system can cut research time by up to 80% compared to manual reviews, allowing security teams to respond to threats more quickly.
NLP also includes Natural Language Generation (NLG), which simplifies technical vulnerability data into business-friendly narratives. This helps bridge the gap between technical teams and executives by explaining risks in both operational and financial contexts. Additionally, it can automate compliance documentation for standards like NIST, ISO 27001, and SOC 2, saving time and improving efficiency.
Dynamic Risk Scoring and Prioritization
Dynamic risk scoring goes beyond merely identifying vulnerabilities by prioritizing them based on context and operational factors. Traditional CVSS scores treat all "Critical" vulnerabilities the same, but AI-powered systems provide more nuanced assessments. These systems combine factors like CVSS severity, asset importance, Exploit Prediction Scoring System (EPSS) data, and live threat activity to create scores that reflect actual urgency.
In November 2024, Databricks introduced "VulnWatch", an AI-based system designed to rank vulnerabilities in third-party libraries. By using large language models like GPT-4o and Llama-3, the system achieved an 85% accuracy rate in identifying critical vulnerabilities and reduced manual triage work by 95%. The Databricks Engineering Team highlighted a key limitation of static scoring systems:
"The CVSS score does not fully capture an organization’s specific context or environment, meaning that a vulnerability with a high CVSS score might not be as critical if the affected component is not in use".
Advanced techniques like semantic embedding further enhance this process by converting CVE descriptions into dense vectors. This allows models to understand the intent and complexity behind threats, even when naming conventions vary. This shift from static assessments to adaptive triage helps organizations focus on what matters most, turning vulnerability management into a precise, efficient operation.
How to Implement AI-Powered Vulnerability Mapping
To implement AI-powered vulnerability mapping, you need to integrate your security tools to achieve real-time visibility across your infrastructure. This approach shifts you away from periodic security snapshots and toward continuous, actionable insights.
Integrating AI Tools with Existing Infrastructure
Begin by linking your AI platform to existing tools like SIEM, XDR, and asset management systems. This integration allows the AI to pull data from multiple sources, automatically correlating vulnerabilities across fragmented tools. For instance, platforms like Security Bulldog work with SOAR systems and internal data sources to create a unified security posture.
The real game-changer here is data correlation across silos. Traditional vulnerability mapping often involves manually piecing together information from separate tools – a process that’s both slow and prone to errors. AI eliminates this hurdle by continuously querying systems, matching CVEs to assets, and identifying patterns. This ensures vulnerabilities are accurately mapped to their respective assets.
Once integration is set, the next step is to establish continuous monitoring.
Configuring Continuous Scanning and Monitoring
Continuous scanning builds on integration by providing real-time asset visibility. Set up monitoring across all environments – endpoints, cloud platforms, and CI/CD pipelines – to detect vulnerabilities as they appear. AI-driven discovery goes a step further by identifying patterns and relationships between systems, configurations, and network behaviors. This is crucial, as organizations currently take an average of 55 days to patch just half of their critical vulnerabilities, while vulnerability exploitation accounts for 14% of all security breaches.
Your system should automatically discover, track, and flag new or modified assets. This real-time approach is critical, especially given the 180% year-over-year increase in vulnerability exploitation.
Enabling Automated Mapping and Visualization
AI-generated vulnerability maps connect assets to threats, business services, and potential risks. These maps go beyond simply displaying vulnerabilities – they guide teams toward precise remediation efforts. For example, effective implementations translate CVSS scores into actionable metrics, such as the percentage of high-risk vulnerabilities resolved within a set timeframe.
To make this data accessible, implement role-based reporting tailored for both technical teams and executives. Using Natural Language Generation (NLG), reports can explain how specific vulnerabilities impact business goals – making them understandable even for non-technical stakeholders. For instance, linking vulnerabilities to critical assets like e-commerce servers can highlight risks in terms of potential revenue loss or downtime.
Automate ticket creation and routing so the system assigns remediation tasks to the right teams based on the affected assets. However, human oversight remains essential for prioritizing deployments and determining remediation strategies. As Praetorian aptly points out:
"Automation handles volume and velocity. Humans handle judgment calls about deployment priorities and remediation strategies".
Benefits and Challenges of AI in Vulnerability Mapping
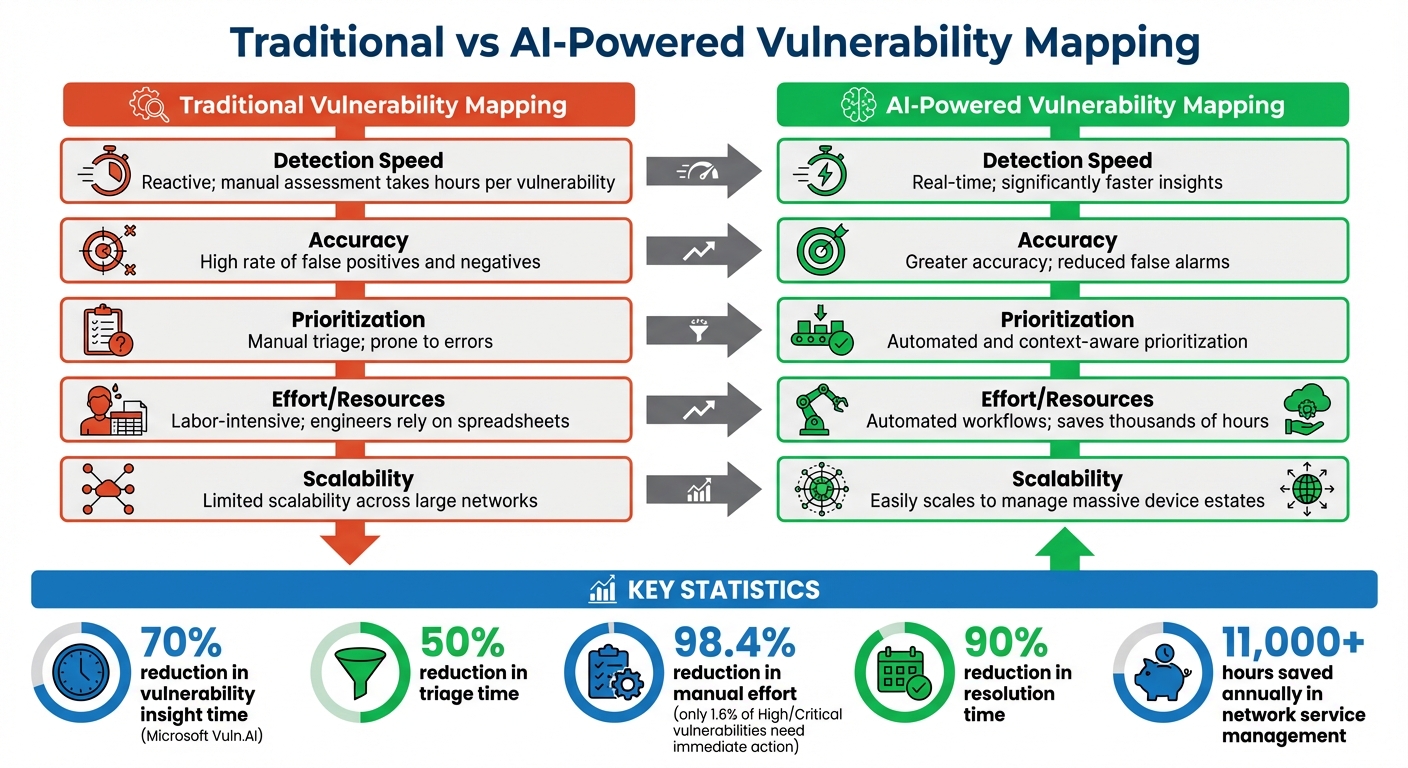
Traditional vs AI-Powered Vulnerability Mapping: Speed, Accuracy and Efficiency Comparison
AI-driven vulnerability mapping offers a mix of advantages and hurdles, building on the strategies and capabilities previously discussed.
Key Benefits of AI-Driven Vulnerability Mapping
AI-powered systems bring speed, precision, and resource efficiency to vulnerability mapping. A standout example is Microsoft’s "Vuln.AI", which automated the process of correlating CVE data with device attributes across a global network. This system drastically cut down detection and triage times, freeing up security engineers to concentrate on critical threats rather than sifting through false positives.
Microsoft’s scale is staggering – they identify over 600 million cybersecurity threats daily. Their AI Ops and Network Infrastructure Copilot is projected to save more than 11,000 hours annually in network service management. As John Burke, CTO and Principal Research Analyst at Nemertes Research, puts it:
"The number one benefit of AI vulnerability management is that it allows IT staff to be more efficient".
AI also excels in context-aware prioritization. Unlike traditional methods that rely heavily on generic CVSS scores, AI systems can map vulnerabilities (CVEs) directly to specific devices by analyzing feeds alongside hardware models and operating system versions. This eliminates the need for manual tracking via spreadsheets, enabling teams to grasp the actual risk posed to their unique setups.
While these benefits are compelling, adopting AI comes with its own set of challenges.
Common Challenges and Recommended Solutions
Despite its advantages, AI implementation isn’t without obstacles. High costs can strain budgets, making it hard for some organizations to justify the investment. Additionally, AI systems require time to learn and adapt to an environment, which can delay initial results. Over time, these systems may also experience "model drift", where their performance declines as they deviate from their initial training.
Large Language Models (LLMs) add another layer of complexity. They can produce inaccurate outputs and are susceptible to manipulation by malicious actors. As Linda Lee, Product Manager II at Microsoft Digital, points out:
"AI is only as good as the data you provide. Much of the success with Vuln.AI came from our dedicated efforts to source comprehensive vulnerability data and device attributes".
To address these challenges, a hybrid approach is often the best solution. Combining automation with human oversight ensures reliability. Blaze Kotsenburg, Software Engineer at Microsoft Digital, explains:
"By combining structured function calls, templated prompts, and data validation, we keep the model focused on producing reliable, actionable insights for vulnerability mitigation".
Regular retraining of AI models is crucial to counteract model drift, and human experts must remain involved to validate AI outputs. Ankit Bansal provides a practical perspective:
"AI’s true power lies in the problem it’s applied to. Start by identifying the most time-consuming or painful task in your organization – then explore how AI can augment or improve it".
Comparison Table: Traditional vs. AI-Powered Mapping
The table below outlines how AI-powered vulnerability mapping stacks up against traditional methods, highlighting both its strengths and the challenges it introduces.
| Feature | Traditional Vulnerability Mapping | AI-Powered Vulnerability Mapping |
|---|---|---|
| Detection Speed | Reactive; manual assessment takes hours per vulnerability | Real-time; significantly faster insights |
| Accuracy | High rate of false positives and negatives | Greater accuracy; reduced false alarms |
| Prioritization | Manual triage; prone to errors | Automated and context-aware prioritization |
| Effort/Resources | Labor-intensive; engineers rely on spreadsheets | Automated workflows; saves thousands of hours |
| Scalability | Limited scalability across large networks | Easily scales to manage massive device estates |
Best Practices for Optimizing AI-Powered Vulnerability Mapping
Correlating with Threat Intelligence Feeds
To make vulnerability data more actionable, it’s essential to integrate AI systems with a variety of threat intelligence sources. Tools like The Security Bulldog, for instance, link to frameworks like MITRE ATT&CK, CVE databases, and curated feeds. This approach adds context that standard vulnerability scanners often miss. AI systems can parse CPE (Common Platform Enumeration) strings, connecting raw CVE data to specific organizational assets. For critical vulnerabilities – like those with network attack vectors and CVSS scores above 9.0 – pipelines should be configured to trigger immediate actions. This integration ensures that the mapping process benefits from timely and context-rich threat data.
Regular Model Training and Process Triage
Keeping AI models accurate over time requires constant updates and refinement. Without this, model performance can degrade. Breaking down vulnerability research into specialized agents – such as Research, Tech Recon, Detection, and Exploit agents – is far more effective than using a single, all-encompassing model. As Janani Mukundan, Principal Research Scientist at Praetorian, highlights:
"Decomposition matters: Breaking the problem into specialized agents outperformed monolithic approaches. Each agent can be optimized, tested, and improved independently."
An actor-critic loop can further enhance results, where a Critic Agent reviews and refines AI outputs. Typically, detection templates require 2–3 iterations to reach production-level quality. For more complex tasks, systems can switch between models – for example, moving from a deep research model to a reasoning-capable one like GPT-5. This flexibility is key, especially for deep research queries, which often take 10–15 minutes to synthesize data from sources like NVD entries and vendor advisories.
Tracking Key Metrics for Continuous Improvement
To ensure that your processes remain effective, tracking performance metrics is non-negotiable. Metrics like MTTR (Mean Time to Respond) and fix rates help validate whether your response times are improving. AI pipelines can also assist by generating pull requests and tickets for human review, with compliance checks ensuring accuracy along the way.
Defining roles within this system is equally important. As Janani Mukundan explains:
"Automation handles volume and velocity. Humans handle judgment calls about deployment priorities and remediation strategies."
While AI is unmatched in its ability to process large datasets and detect patterns, the final decisions – especially those involving deployment and remediation – should always involve human judgment. This balance ensures both speed and reliability.
Conclusion: The Future of AI in Real-Time Vulnerability Mapping
AI is reshaping how organizations tackle vulnerabilities, moving from manual tracking methods to systems that work autonomously and collaboratively. This shift isn’t just incremental – it’s a leap forward in efficiency and capability. Real-world implementations have already shown how AI can streamline processes and provide faster, more accurate results.
What’s next? The future of vulnerability mapping is heading toward autonomous remediation workflows. In simpler terms, AI won’t just identify vulnerabilities – it will help fix them. These workflows will make patching and mitigation faster and more seamless. At the same time, natural language interfaces will allow security teams to ask complex questions about network data and receive clear, actionable answers. Meanwhile, AI agents will interact with each other to provide contextual insights, eliminating the need for constant human input.
This evolution builds on the continuous, real-time insights already in play. Brian Fielder, Vice President at Microsoft Digital, highlights this dual-edged nature of AI:
"While AI enables amazing capabilities for knowledge workers, it also increases the threat landscape, since bad actors using AI are constantly probing for vulnerabilities. Vuln.AI helps keep Microsoft safe by identifying and accelerating the mitigation of vulnerabilities."
With Microsoft detecting over 600 million cybersecurity threats daily, the scale of the challenge is staggering. Intelligent automation is no longer optional – it’s essential. Tools like The Security Bulldog use AI-powered natural language processing to sift through open-source intelligence from CVE databases and the MITRE ATT&CK framework. By automating this research-heavy phase, teams can focus their energy on actual remediation. Linda Lee, Product Manager II at Microsoft Digital, points out the importance of data quality in this process:
"AI is only as good as the data you provide. Much of the success with Vuln.AI came from our dedicated efforts to source comprehensive vulnerability data and device attributes."
These advancements highlight a major shift – from reactive cybersecurity methods to a proactive, context-aware approach. While AI handles the heavy lifting of volume and speed, human expertise remains essential for critical decisions, such as prioritizing deployments and fine-tuning remediation strategies. The true power lies in combining the precision of machines with the judgment of people. Together, they’re driving the next wave of cybersecurity innovation.
FAQs
What data does AI need to map vulnerabilities accurately in real time?
AI depends on high-quality, real-time data from multiple sources to identify vulnerabilities effectively. The key inputs it relies on include:
- Vulnerability databases like CVE (Common Vulnerabilities and Exposures), which catalog known security flaws.
- Threat intelligence feeds that provide updates on emerging threats and attack patterns.
- Network logs that capture activity across systems, offering clues about potential weaknesses.
- Active monitoring systems, which continuously track network activity to detect unusual behavior.
By combining these data streams, AI can deliver precise and timely insights into potential threats, helping organizations stay ahead of security risks.
How do you connect AI vulnerability mapping to SIEM, XDR, and SOAR tools?
Integrating AI-driven vulnerability mapping with tools like SIEM, XDR, and SOAR takes security operations to the next level. By feeding AI-generated threat intelligence and vulnerability data into these systems, organizations can improve detection capabilities, streamline responses, and enhance automation.
AI tools such as The Security Bulldog analyze open-source intelligence, assess risks, and prioritize them effectively. These tools often output data in widely accepted formats like JSON or STIX/TAXII, ensuring smooth integration with existing security platforms. The result? Improved alert accuracy, automated workflows, and a more efficient approach to managing vulnerabilities – all contributing to stronger security outcomes.
How can teams prevent AI model drift and keep results trustworthy over time?
To keep AI models reliable and accurate, it’s important to monitor and update them regularly. Retraining models with new, high-quality data helps them stay aligned with evolving threats and patterns, minimizing drift. Keeping an eye out for issues like data poisoning or bias is equally critical to ensure the model’s accuracy. Adding human oversight to the process provides an extra layer of validation, improving trust in the outputs. Ultimately, consistent updates and maintaining data quality are key to effective AI-driven vulnerability mapping.