Is the SOC tech stack missing a management layer between the SIEM and SOAR?
Modern SOCs rely on SIEM for threat detection and SOAR for automated responses. But many teams struggle with inefficiencies caused by a gap between these tools. Analysts face high alert volumes, fragmented workflows, and manual processes that slow down threat response. A management layer could solve these issues by bridging SIEM and SOAR, enriching alerts, reducing noise, and automating investigations.
Key Takeaways:
- SIEM collects and analyzes data for threat detection.
- SOAR automates responses but depends on structured data.
- SOCs handle thousands of alerts daily, with 50-99% being false positives.
- A management layer can:
- Enrich alerts with context (e.g., threat intelligence, asset data).
- Group related alerts to reduce noise.
- Automate investigations and risk scoring.
- Save analysts time by preparing actionable insights.
The Security Bulldog is one example of a tool addressing this gap. Its AI-driven platform integrates SIEM and SOAR, reducing manual tasks and improving response times. Starting at $850/month, it promises faster detection, streamlined workflows, and cost savings for SOC teams.
SOAR vs SIEM – What’s the Difference? (Pros and Cons)
sbb-itb-9b7603c
Challenges in SIEM-SOAR Integration
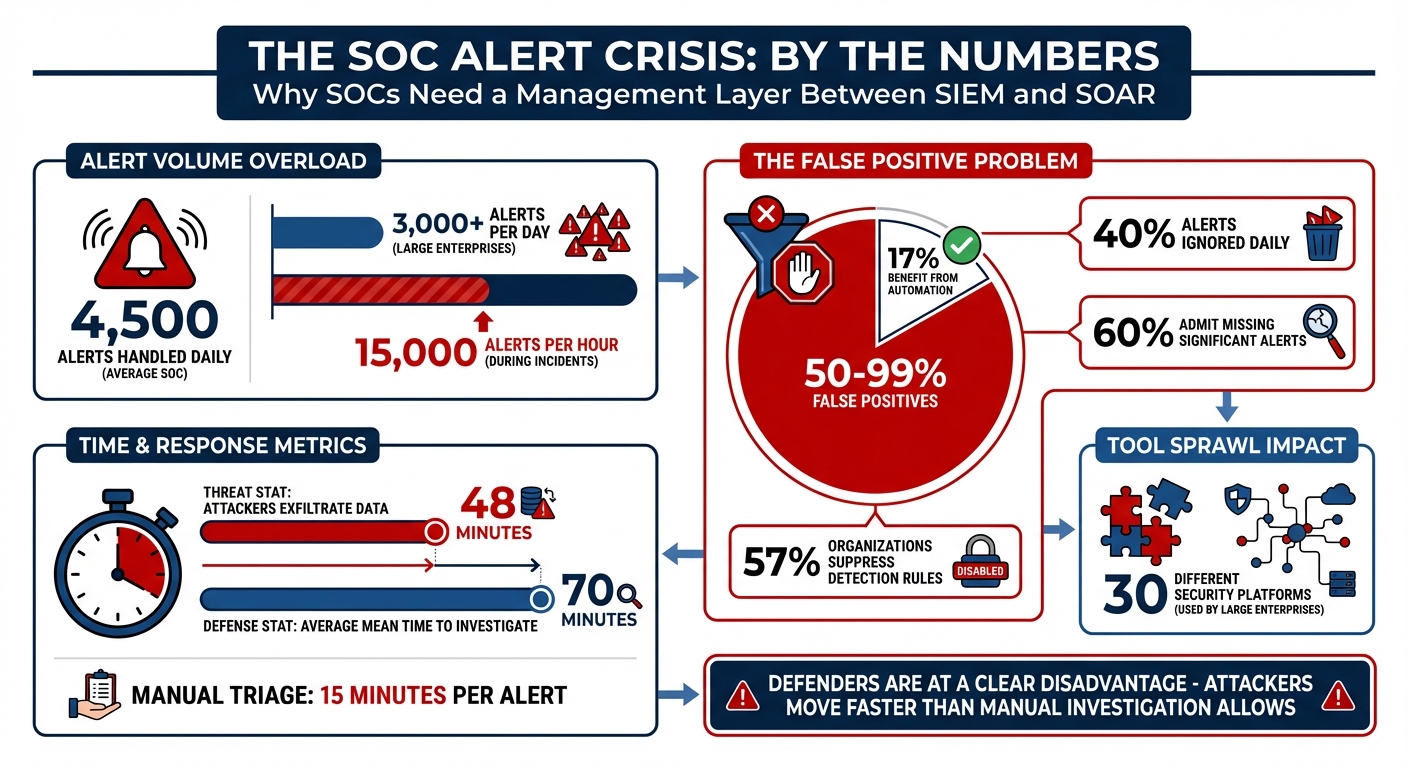
SOC Alert Management Statistics: Volume, False Positives, and Response Times
When SIEM and SOAR systems don’t work seamlessly together, it creates three major challenges that slow down threat response and overwhelm security teams.
Siloed Operations and Workflow Disconnects
SIEM and SOAR often function as separate systems. SIEM focuses on detecting threats but lacks the ability to act on them. SOAR, on the other hand, handles response actions but relies on accurate, well-structured data to operate effectively. This disconnect forces analysts to manually bridge the gap, triaging SIEM alerts before they can feed into SOAR workflows. The result? Endless context switching between SIEM, EDR, and IAM systems, turning tasks that should take 10 minutes into hour-long challenges.
Ajmal Kohgadai, Director of Product Marketing at Prophet Security, captures the problem well:
The collective result [of tool sprawl] is an integration nightmare that’s making security teams progressively less effective.
The average large enterprise uses nearly 30 different security platforms generating alerts. Each platform comes with its own query language and data format, adding to the complexity. This fragmentation not only wastes time but also creates blind spots where critical threats can go unnoticed. Combined with high alert volumes, these inefficiencies only add to the strain on already stretched teams.
High Alert Volumes and Analyst Overload
The sheer number of alerts is overwhelming for SOC teams. On average, SOCs handle 4,500 alerts daily, with larger enterprises seeing over 3,000 alerts per day. During incidents or misconfigurations, these numbers can skyrocket to 15,000 alerts per hour. Alarmingly, between 50% and 99% of these alerts are false positives, yet only 17% of alerts benefit from automation. The rest require manual review, which is simply unmanageable at scale.
This overload leads to critical alerts being ignored. Security teams admit to ignoring 40% of alerts daily, and 60% acknowledge having missed alerts that later turned out to be significant. To cope, 57% of organizations suppress detection rules, effectively choosing to overlook potential threats to avoid drowning in noise. But with attackers capable of exfiltrating data in as little as 48 minutes, and the average Mean Time to Investigate sitting at 70 minutes, defenders are at a clear disadvantage. Beyond the alert flood, integrating diverse tools adds another layer of complexity.
Limited Interoperability Without Custom Engineering
Integrating SIEM and SOAR without heavy custom development is a daunting task. Security tools like firewalls, IDS, and antivirus systems often produce incompatible data formats, requiring extensive log parsing and normalization efforts. Without standardized formats like JSON or CEF, SOAR platforms struggle to orchestrate workflows effectively. Even when integrations exist, they often rely on custom coding that breaks whenever vendors update their software.
A real-world example comes from Lennar’s SOC team, which faced this issue in early 2026. Their previous SOAR solution, XSOAR, failed to integrate with their security stack, forcing analysts to spend countless hours on manual phishing remediation. Daniel Gross, Senior Operations Analyst at Lennar, shared:
The phishing remediations we’ve done with Torq have significantly reduced the amount of time put into phishing remediations.
Bloomreach encountered a similar roadblock. Their traditional SOAR required developer-level expertise for every workflow, limiting automation to a small group of specialists. Chris Talevi, Deputy CISO at Bloomreach, explained:
We wanted everybody on the team to be able to build automations – not just developers. With traditional SOAR, that wasn’t possible.
This reliance on custom engineering forces skilled analysts to spend their time maintaining workflows and fixing integrations instead of focusing on actual threats. These challenges underscore the need for a better way to streamline SOC workflows and reduce the burden on security teams.
The Case for a Management Layer
The challenges posed by SIEM-SOAR systems highlight the need for a dedicated intermediary that bridges the gap between detection and response. This management layer is designed to sift through raw, noisy alerts and convert them into actionable insights before they reach analysts or trigger automated workflows. Instead of simply funneling alerts into ticketing systems, this layer processes, enriches, and prioritizes signals. Let’s dive into the core functions, advantages, and AI-driven approaches that define this concept.
What Would a Management Layer Do?
A management layer fills the gaps left between SIEM and SOAR systems. It standardizes diverse alerts and enriches them with contextual data from sources like CMDBs, asset inventories, and threat intelligence feeds. By doing this, it ensures that alerts are not just raw signals but meaningful, context-rich cases. Another key function is deduplication – linking related alerts into a single case rather than creating multiple tickets for the same underlying issue.
But it doesn’t stop there. The layer also conducts automated investigations, pulling data from various sources to construct a detailed timeline of events. Using AI, it translates complex technical logs into concise summaries that are easy for humans to understand. Risk scoring logic is then applied, analyzing factors such as IP reputation, odd login patterns, and MFA status. This helps determine whether an alert should be ignored, escalated, or enriched further. By handling these tasks, the management layer directly addresses the overwhelming alert volumes and analyst fatigue that plague many SOCs.
Hamza Razzaq, a cybersecurity expert, sums it up perfectly:
Alert routing without intelligence is not automation. It is amplification. Signals move faster, but understanding does not.
Currently, manual triage can take about 15 minutes per alert, with analysts jumping between EDR tools, directory services, and threat intel platforms. A management layer eliminates this inefficiency, enabling analysts to begin with a fully assembled investigation package, saving time and effort.
Benefits of an Intermediary Layer
The standout advantage of this layer is its ability to break the direct link between alert volume and human effort. AI agents within the management layer can handle hundreds of alerts simultaneously, ensuring consistent quality without requiring a proportional increase in SOC staffing.
Organizations that have adopted AI-powered management layers report impressive results. Mean Time to Investigate (MTTI) can drop from over 25 minutes to just 3–4 minutes. More complex investigations that previously took hours can now be completed in as little as 9 minutes, with greater depth and accuracy. Additionally, by grouping related alerts into single incidents, the layer prevents "queue bloat", allowing analysts to focus on behaviors rather than isolated symptoms.
Another major benefit is the ability to make decisions with context. Advanced management layers can identify whether a similar IP or user has triggered alerts before, appending new data to an existing case rather than creating duplicates. This drastically reduces alert fatigue and ensures teams focus on genuine threats rather than chasing redundant signals.
AI-Powered Solutions for the Management Layer
AI is central to the success of this management layer. These systems leverage agentic AI, which uses adaptive reasoning to decide which tools to query based on the alert type, avoiding rigid, one-size-fits-all playbooks. Ajmal Kohgadai, Director of Product Marketing at Prophet Security, explains:
AI does not replace SOAR or SIEM. It complements them by orchestrating investigations and routing response actions through existing systems. AI handles the reasoning, while SOAR executes.
In this hybrid model, AI takes on the heavy lifting – gathering and synthesizing data – while humans focus on making critical risk decisions and approvals. Industry experts predict that AI will manage around 60% of SOC workloads within the next three years. This shift is redefining the role of junior analysts, turning them into "investigation reviewers" who gain experience by analyzing AI-generated narratives instead of performing repetitive tasks.
| Function | Description | Outcome |
|---|---|---|
| Enrichment | Adds CMDB, Identity, and Threat Intel data | Reduces manual context switching |
| Deduplication | Groups related alerts into one incident | Prevents alert storms and queue bloat |
| AI Synthesis | Converts logs into human narratives | Speeds up analyst understanding |
| Risk Scoring | Assigns numerical values to alert signals | Enables consistent, automated decisions |
| Stateful Correlation | Checks for repeated events over time | Avoids duplicate case creation |
How The Security Bulldog Bridges the SIEM-SOAR Gap
The Security Bulldog steps in as a smart, AI-driven solution to bridge the gap between Security Information and Event Management (SIEM) tools and Security Orchestration, Automation, and Response (SOAR) systems.
Acting as an AI-powered management layer, The Security Bulldog connects SIEM detection with SOAR execution. Its standout feature is a proprietary natural language processing (NLP) engine that processes millions of cybersecurity documents every day. From CVE databases and news updates to podcasts and the MITRE ATT&CK framework, this engine transforms a massive amount of raw data into clear, actionable intelligence that’s easy to understand. It also automates enrichment tasks, eliminating the need for manual searches.
This integration helps solve workflow issues by tying together detection and response. The platform works seamlessly with existing tools, enabling smooth data sharing between SIEM systems, SOAR platforms, asset management software, and ticketing tools like ServiceNow and Jira. By cutting down on the need to switch between multiple dashboards, The Security Bulldog ensures a more streamlined and efficient process.
Key Features of The Security Bulldog
One of the platform’s biggest strengths is its ability to automate the contextualization of data. The NLP engine continuously scans open-source intelligence (OSINT) to build a curated knowledge base tailored to your industry, IT setup, and specific workflows. Teams can set up custom feeds for individual members, ensuring each analyst gets information relevant to their role. The platform also integrates with CVE and Known Exploited Vulnerabilities (KEV) databases, helping teams prioritize the most critical vulnerabilities.
In addition to intelligence gathering, The Security Bulldog includes built-in tools for collaboration, making it easier for teams to share information and coordinate incident responses. It directly integrates with SOAR platforms, speeding up remediation by feeding curated intelligence into existing playbooks. SOC teams can start saving time on research immediately, without needing a lengthy implementation process.
Benefits for SOC Teams
The Security Bulldog brings measurable improvements to Security Operations Center (SOC) workflows. Organizations using the platform report an 80% reduction in manual research time right from the start. Additionally, remediation times improve by 30%, helping teams tackle ticket backlogs in half the usual time. Threat detection speeds up as well, with over an 80% reduction in detection times, allowing analysts to act on alerts much faster.
These efficiency gains translate into significant cost savings. The platform boasts a 600x return on investment (ROI) for enterprise cybersecurity teams by cutting down the time analysts spend switching between tools. As the creators of The Security Bulldog put it:
We don’t need more data and alerts: we need better answers.
By presenting complex technical information in an easy-to-digest format, the platform reduces the cognitive load on analysts. This means teams can make better decisions without needing to expand their headcount.
Plans and Pricing
The Security Bulldog offers flexible pricing options to cater to different SOC needs, ensuring teams can scale as required.
- Enterprise Plan: Priced at $850/month (or $9,350 annually), this tier supports up to 10 users. It includes AI-powered OSINT collection, access to a CVE database, MITRE ATT&CK integration, and basic connections with SIEM, SOAR, and ticketing tools.
- Enterprise Pro Plan: Designed for larger teams, this plan offers custom pricing through a demo consultation. It includes advanced SIEM and SOAR integrations, metered data, 24/7 dedicated support, custom onboarding, and ongoing training.
Both plans come with a free trial, allowing SOC teams to experience the platform’s benefits – such as reduced manual research – before committing.
Implementing a SIEM-SOAR Management Layer
Introducing a management layer between your SIEM and SOAR allows you to enhance your existing infrastructure without overhauling it. This layer works alongside your current tools, pulling data via APIs and avoiding disruptions to ongoing operations.
Assessing Your Current SOC Maturity
Start by evaluating your SOC’s maturity. Create a detailed map of your current setup, including all alert sources (like EDR, cloud, and identity systems), your SIEM, threat intelligence feeds, and action tools such as SOAR and ticketing systems.
Next, review your processes. Do you have structured, repeatable response playbooks? These are critical for effective automation. As nFlo aptly points out:
Deploying SOAR in an organization that does not have clearly described response playbooks will result in disappointment – automating chaos only produces faster chaos.
Identify bottlenecks where analysts lose time switching between consoles or manually gathering data. Research indicates that nearly 40% of alerts go uninvestigated, and false positives account for 45% to 70% of alerts. Mature SOCs typically achieve a Mean Time to Detect (MTTD) of less than 24 hours and a Mean Time to Respond (MTTR) of under 4 hours.
Once you understand your SOC’s maturity, you can focus on integrating targeted threat intelligence and automation.
Integrating Threat Intelligence and Automation
Begin by addressing a specific use case to show measurable results. Ensure your SIEM uses standard log formats (such as syslog, JSON, or CEF) and that both your SIEM and SOAR support RESTful or SOAP APIs for real-time data sharing.
Set up a secure, bidirectional API flow. Use API tokens or OAuth for secure access, enabling your SIEM to send alerts to your SOAR and allowing your SOAR or EDR to execute actions like isolating devices or revoking credentials. Configure filters to minimize unnecessary queries to third-party threat intelligence APIs.
Test the integration in a sandbox environment with simulated alerts before moving to production. Automate low-risk actions, like updating tickets, while requiring manual approval for high-risk actions, such as isolating critical servers.
Once your API flows and automation rules are live, track their impact by comparing key performance metrics before and after deployment.
Measuring Success and Optimization
After implementation, measure improvements using specific metrics. Record baseline statistics for MTTD, MTTR, and analyst effort per case before integration. Post-integration, these numbers should show significant improvement – tasks that once took hours might now take just 9 minutes.
Fine-tune your system to reduce false positives from the common 45–70% range to below 5%. Another key metric is Mean Time to Investigate (MTTI), which measures the time from acknowledging an alert to completing the investigation. A well-implemented management layer can cut MTTI from over 25 minutes to just 3–4 minutes. Additionally, reclaim analyst time by automating manual triage, potentially freeing up 25% of their capacity.
Keep an eye on the AI feedback loop. The management layer should help identify false positives and recommend suppression logic or rule adjustments for your SIEM. This continuous learning process ensures your SOC doesn’t just get faster – it becomes smarter over time.
Conclusion
The gap between SIEM and SOAR is a pressing challenge for modern SOCs. With overwhelming alert volumes leading to ignored warnings and missed critical incidents, the call for a smarter management layer is impossible to overlook.
This management layer acts as the glue that binds your SOC tools into a cohesive system. It breaks the link between alert volume and human workload, enabling AI agents to handle hundreds of alerts simultaneously. Meanwhile, your analysts can focus on making informed decisions and tackling strategic priorities. As Ajmal Kohgadai, Director of Product Marketing at Prophet Security, puts it:
SOAR was the right idea at the wrong level of abstraction. Automating individual actions was a necessary step, but it was never going to solve the hard part of security operations: the reasoning.
The results speak for themselves. Organizations implementing these improvements report sharp reductions in MTTI and save an average of $1.76 million per breach through advanced automation. For SOC analysts, who often face burnout rates between 63% and 76%, this is a game-changer. Analysts currently spend 10 to 15 hours a week on repetitive tasks that a management layer could easily handle.
To address this challenge, The Security Bulldog offers the intelligent orchestration SOCs need. Its AI-powered NLP engine connects seamlessly with your SIEM and SOAR systems, creating a unified, smarter SOC stack. Starting at $850/month for small teams, it integrates threat intelligence from sources like MITRE ATT&CK, CVE databases, and open-source feeds while enabling smooth communication with response tools. For larger organizations, the Enterprise Pro plan delivers custom SIEM and SOAR integrations tailored to your unique environment.
Don’t let critical alerts slip through the cracks. The future of security operations lies in combining human expertise with advanced AI orchestration. Take the first step by evaluating your SOC’s current state, pinpointing inefficiencies, and implementing a management layer to shift from reactive firefighting to proactive defense.
FAQs
What is a SOC management layer between SIEM and SOAR?
A SOC management layer acts as the connecting link between SIEM (which specializes in detecting threats by analyzing log data) and SOAR (designed to automate incident response). It plays a key role in improving workflows, enabling smoother data sharing, and boosting overall operational efficiency. By leveraging AI or automation, this layer simplifies key processes like threat detection, investigation, and response, cutting down on manual tasks. It also enhances compatibility between various security tools, helping to maximize the effectiveness of the SOC.
How does a management layer cut false positives and alert noise?
A management layer sitting between SIEM and SOAR can significantly cut down on false positives and alert noise. How? By using AI-driven automation to filter, prioritize, and triage alerts before they reach analysts. This layer helps separate real threats from harmless anomalies, reducing the clutter that often overwhelms security teams.
By correlating signals, adding context, and automating responses to low-priority issues, it simplifies workflows and keeps analysts focused on the alerts that truly matter. The result? Less alert fatigue and more efficient handling of genuine security incidents.
What should we measure to prove the layer improved SOC performance?
To demonstrate how adding a management layer between SIEM and SOAR can boost SOC performance, focus on tracking a few critical metrics. Start with Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) – these measure how quickly threats are identified and addressed. Keep an eye on alert accuracy, including false positives and negatives, to see if the system is flagging the right issues.
Additionally, evaluate alert volume and noise levels to determine if the management layer helps cut down on unnecessary alerts and reduces overload. Positive changes in these metrics suggest better responsiveness, less alert fatigue, and smoother integration of workflows.