How AI Enhances Temporal Threat Severity Analysis
- Dynamic Risk Assessment: Unlike static scoring systems, AI updates threat severity in real-time based on changing factors like exploit tools and patch availability.
- Improved Accuracy: Machine learning models achieve over 94% accuracy in classifying threats, reducing false positives and prioritizing real risks.
- Faster Response: AI-powered systems analyze network alerts in minutes, enabling rapid detection and mitigation of potential attacks.
- Efficient Resource Use: Automation helps smaller teams handle high alert volumes, cutting manual reviews and improving response times.
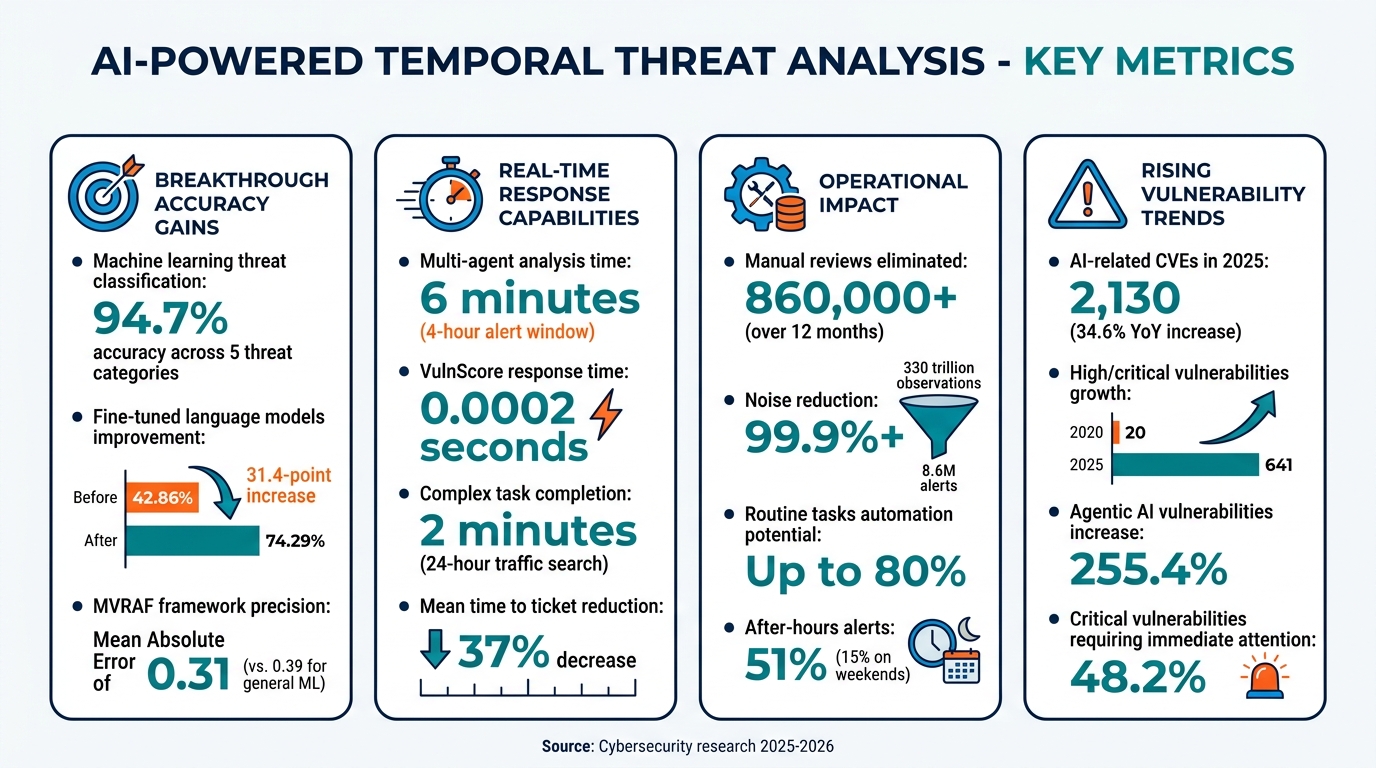
AI-Powered Temporal Threat Analysis: Key Performance Metrics and Impact Statistics
AI Technologies That Power Temporal Threat Severity Analysis
Machine Learning Algorithms for Threat Modeling
Modern threat modeling leverages ensemble methods, combining multiple algorithms to track and predict how threats evolve. For instance, Random Forest and Gradient Boosting classifiers, when paired with temporal sequence modeling, achieve 94.7% classification accuracy across five distinct threat categories. These techniques highlight how combining algorithms enhances the ability to detect and classify threats over time.
In addition to these traditional methods, fine-tuned language models using QLoRA (Quantized Low-Rank Adaptation) have made significant strides in temporal attack detection. Research by Ron F. Del Rosario in 2025 showed that iterative fine-tuning with over 80,000 cybersecurity examples and 35,000 synthetic traces boosted detection accuracy from 42.86% to 74.29% – a remarkable 31.4-point improvement. As Del Rosario emphasized:
"Training data composition fundamentally determines behavior".
These advancements strengthen temporal risk models, allowing them to adapt to an ever-changing threat landscape.
Natural Language Processing (NLP) for Contextual Intelligence
While machine learning excels at prediction, NLP adds depth by extracting context from diverse datasets. NLP engines process open-source intelligence, enabling context-aware threat analysis that moves beyond generic alerts. For example, the Security Bulldog’s NLP engine synthesizes cyber intelligence to reveal not just what a threat is, but why it matters within a specific environment.
Marco Graziano of Graziano Labs Corp showcased the power of NLP in April 2025. His generative multi-agent system analyzed a four-hour network alert window, identifying two high-severity patterns, such as outdated nginx servers communicating at regular five-minute intervals. The system completed its analysis in just six minutes, producing a structured report with prioritized remediation steps after 14 interaction turns. Graziano explained:
"By combining natural language interaction with contextual memory and procedural reasoning, these agents become a powerful interface for SOC workflows".
This capability enhances the ability of temporal risk models to adapt and respond to evolving threats.
Real-Time Data Collection and Processing
Real-time data collection forms the backbone of continuous monitoring, a critical component of temporal threat analysis. Systems like OpenTelemetry and Kafka-based pipelines provide the infrastructure needed for continuous data streams, ensuring up-to-date threat evaluations. VulnScore, a real-time prioritization tool, demonstrates this efficiency with response times as quick as 0.0002 seconds.
Multi-agent systems now use standardized protocols like the Model Context Protocol (MCP) to connect AI agents with external data sources, such as NIST vulnerability databases and WHOIS servers. These systems can handle complex tasks – like locating specific source IPs across 24 hours of network traffic – in roughly two minutes. This speed is crucial, especially as AI-related CVEs surged to 2,130 in 2025, marking a 34.6% year-over-year increase. High- and critical-severity vulnerabilities grew from just 20 in 2020 to 641 in 2025.
These real-time capabilities ensure temporal risk models remain responsive in an increasingly dynamic threat environment.
sbb-itb-9b7603c
How AI Is Used in Temporal Threat Severity Analysis
Dynamic Risk Scoring Over Time
AI systems are changing the game when it comes to assessing threat severity. Instead of relying solely on static CVSS scores, they continuously update risk assessments as new information becomes available. For example, platforms now combine temporal threat intelligence tools, like the Exploit Prediction Scoring System (EPSS), with AI-driven real-time risk ratings and user-defined asset priorities to calculate the likelihood of exploitation in real time.
Multi-agent architectures play a key role in this process. These systems use specialized agents that adapt their strategies when initial searches come up empty. For instance, they might extend the search window from two hours to 24 hours or adjust parameters to uncover relevant patterns. Intermediate findings are stored in shared memory so that threat scores can be updated as new network data or intelligence surfaces. This approach enables near-real-time severity calculations, which is critical for staying ahead of potential threats.
Early Threat Detection and Mitigation
The dynamic scoring capabilities of AI don’t just stop at risk assessment – they also pave the way for early detection of emerging threats. A great example of this was demonstrated in April 2025 by Marco Graziano of Graziano Labs. Using a multi-agent system built on the Pydantic AI framework, the system analyzed network alerts within a four-hour period and completed its investigation in just six minutes. It executed 13 procedures to flag a suspicious 5:1 outbound-to-inbound data ratio, a key sign of possible data exfiltration.
This kind of speed is essential, especially given the rising number of vulnerabilities. Trend Micro highlighted this urgency in their research:
"Static, compliance‑driven measures are no longer sufficient. Security teams must evolve toward adaptive, layered strategies capable of anticipating and mitigating emerging risks".
Case Study: The Security Bulldog in Action
The Security Bulldog is a perfect example of how AI-powered tools are transforming threat analysis. This platform uses natural language processing (NLP) to analyze open-source cyber intelligence from sources like the MITRE ATT&CK framework and CVE databases. By applying semantic analysis, it identifies not only the nature of a threat but also how it could impact your specific IT environment.
Tailored for smaller teams (up to 10 users), The Security Bulldog’s Enterprise plan is priced at $850/month or $9,350/year. It offers AI-driven OSINT collection with custom feeds that align with your infrastructure. The platform also integrates seamlessly with existing SOAR and SIEM tools, allowing analysts to import internal data and export findings without disrupting current workflows. By automating the research process and delivering actionable, context-aware insights, The Security Bulldog helps teams respond faster – an essential feature in light of the 255.4% increase in agentic AI vulnerabilities reported in 2025.
Benefits of AI-Powered Temporal Threat Severity Analysis
Better Accuracy and Threat Understanding
AI-powered temporal analysis significantly reduces false positives by analyzing how threats evolve over time. Traditional methods often misinterpret legitimate activities as malicious due to their inability to understand behavioral context. In contrast, AI uses temporal intelligence to map timelines and identify patterns, helping security teams spot risks that static analysis might miss.
This technology also bolsters forensic investigations by capturing evidence with precise timestamps. These detailed records are invaluable for reconstructing attack sequences and understanding how threats unfold. Security teams can pinpoint exactly how an attacker navigated the network, what data was compromised, and the time of each event.
This improved understanding of threats enables faster and more informed decision-making.
Faster Decision-Making and Response Times
When attackers can cause extensive damage in mere minutes, speed is everything. David Cass, CISO at GSR, highlighted this urgency:
"I’ve had to work as an expert with numerous companies where literally, in under 30 minutes, they’ve lost north of $25 million".
AI accelerates response times by automating incident triage and enriching data in real time. By integrating with SOAR platforms, AI handles tasks like data enrichment and executing playbooks automatically. Naveen Balakrishnan, Managing Director at TD Securities, emphasized this efficiency:
"The AI tools right now are very effective, where now you can get a skilled responder to investigate within minutes".
It’s estimated that AI could automate up to 80% of routine security tasks, allowing analysts to focus on more critical tasks like strategic planning and advanced threat detection.
More Efficient Use of Cybersecurity Resources
For smaller teams overwhelmed by a flood of alerts, AI offers a lifeline. In March 2026, Arctic Wolf reported that its Aurora Platform, powered by "Alpha AI", triaged 10% of all security alerts over a 12-month period. This automation eliminated over 860,000 manual reviews, cutting the mean time to ticket by 37%. The platform also reduced 330 trillion raw observations to just 8.6 million actionable alerts, achieving a noise reduction rate of over 99.9%.
This efficiency is especially critical since 51% of alerts occur outside regular business hours, with 15% happening on weekends. AI provides constant, round-the-clock coverage, eliminating the need for large and costly night-shift teams. However, as David Cass pointed out:
"AI is solving some of our lower-level problems for our security staff, but is it a replacement for them? Not really. Because again, you still need human intervention and you still need people that understand how your organization works".
How Microsoft Uses AI for Threat Intelligence & Malware Analysis
Conclusion: The Future of Temporal Threat Severity Analysis with AI
As cyber threats grow more sophisticated, AI-driven temporal threat severity analysis is becoming a critical tool for staying ahead of attackers. With the number of CVEs (Common Vulnerabilities and Exposures) climbing rapidly, traditional methods are struggling to keep up. AI tackles this problem by moving beyond simple, binary classifications of threats to deliver more nuanced, multi-layered assessments that reflect the complexity of today’s attack vectors.
The next wave of AI advancements will focus on predicting and mitigating emerging threats before they materialize. Wanru Shao from Northeastern University highlighted this forward-looking approach:
"Future work will extend MVRAF to incorporate temporal vulnerability trends, develop predictive models for emerging threat patterns, and integrate with automated patch management systems for real-time security posture optimization".
Frameworks like MVRAF are already demonstrating improved accuracy, with a Mean Absolute Error of 0.31, outperforming general machine learning predictors that average 0.39. This leap in precision paves the way for tools that deliver actionable insights in real time.
Platforms such as The Security Bulldog (https://securitybulldog.com) are operationalizing these advancements. By combining a proprietary NLP engine with live intelligence from sources like MITRE ATT&CK and CVE databases, these tools help security teams identify and prioritize the 48.2% of vulnerabilities that demand immediate attention. This capability allows organizations to optimize their security posture in ways traditional methods simply cannot.
To use resources effectively, security teams should focus on vulnerabilities with low attack complexity and no privilege requirements, which tend to have the highest severity scores – averaging 7.32 on the CVSS scale. AI’s ability to map attack vectors and evaluate confidentiality, integrity, and availability (CIA) impacts enables organizations to pinpoint "risk hotspots" and allocate resources where they matter most. Importantly, this approach doesn’t aim to replace human analysts but rather to empower them by handling the heavy lifting of data analysis and pattern recognition.
As the volume and sophistication of threats continue to grow, AI-powered temporal threat severity analysis is set to become the cornerstone of effective cybersecurity strategies. By augmenting human expertise, AI equips early adopters with the tools they need to outpace emerging threats and safeguard their systems more effectively.
FAQs
What does ‘temporal’ threat severity mean?
‘Temporal’ threat severity examines how the risk level of cybersecurity threats shifts over time. It considers factors such as the availability of exploits, the importance of affected assets, and updates in threat intelligence. This time-sensitive approach allows organizations to prioritize their responses and adjust strategies to address evolving risks more effectively.
How does AI update severity when exploits or patches change?
AI constantly adjusts severity levels by examining changing threat landscapes, vulnerabilities, and system conditions. It processes real-time data to reevaluate risks, taking into account shifts like new exploit techniques, updated attack strategies, or the effectiveness of patches. This approach keeps severity scores relevant and helps security teams focus on the most urgent issues. With continuous monitoring and analysis, AI reacts much faster than traditional static methods, ensuring responses align with the latest threat intelligence.
What data is needed for AI-based temporal scoring in a SOC?
AI-driven temporal scoring in a Security Operations Center (SOC) relies on time-stamped data – things like historical incident records, logs, and event timelines – to spot patterns and trends over time. By incorporating contextual threat intelligence, such as vulnerability details, threat actor activities, and detailed reports, the analysis becomes even more effective. Using Natural Language Processing (NLP), insights can be pulled from unstructured text, adding depth to datasets. This helps create precise timelines, recognize behavioral patterns, and even predict risks proactively.