Uncategorized
Using visuals to communicate threat intelligence effectively
Turn raw alerts into clear, actionable insights with graphs, timelines, and heatmaps—tailored dashboards for analysts, executives, and teams.
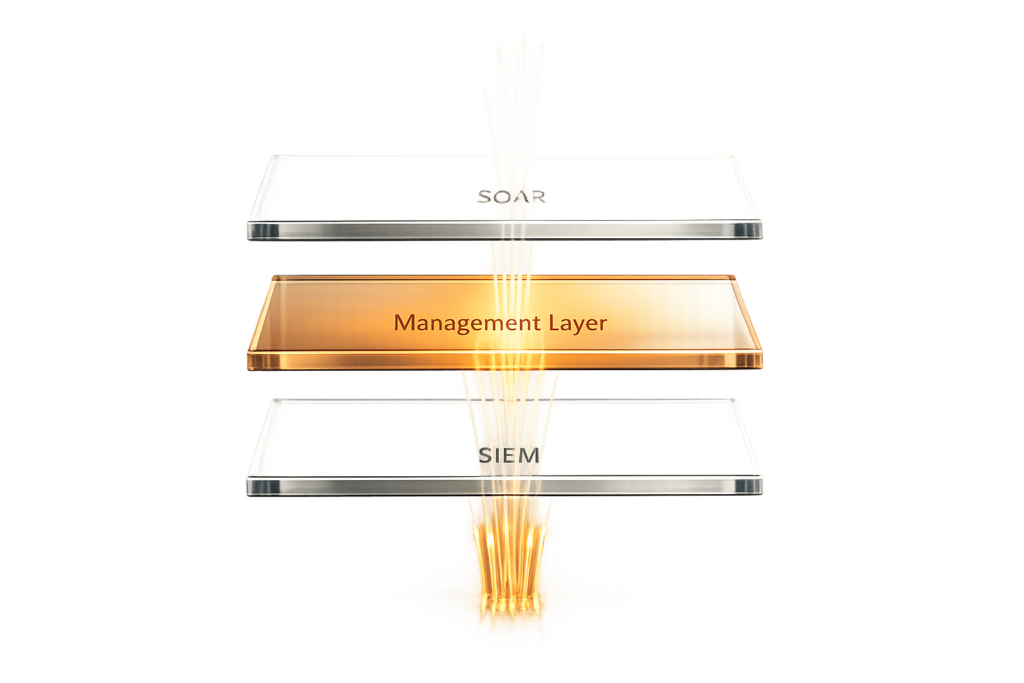
Read MoreIs the SOC tech stack missing a management layer between the SIEM and SOAR?
How a management layer between SIEM and SOAR can cut alert noise, enrich context, automate investigations, and speed SOC response.
Read MoreSOC Capacity and The Security Bulldog: How Many Alerts Can Your Team Really Handle?
SOC teams must measure true capacity, prioritize alerts by business risk, and use AI automation to cut false positives and stop analyst burnout.
Read MoreHow Spunk and The Security Bulldog Work Together
Combining Splunk telemetry with AI-driven OSINT to speed investigations, cut manual research, and reduce MTTR for security teams.
Read MoreHow AI Powers Real-Time Vulnerability Mapping
How AI enables continuous vulnerability mapping: real-time detection, context-aware prioritization, and automated remediation with human oversight.
Read MoreHow Anomaly Detection Improves Threat Prediction Accuracy
Machine-learning anomaly detection spots unusual behavior to detect zero-day attacks, reduce false positives, speed response, and lower breach costs.
Read MorePassword Strength Checker
Check your password strength instantly with our free tool. Get a score, feedback, and tips to make your passwords unbreakable!
Read MoreHow to Use Microsegmentation and AI to Stop Lateral Movement
Learn how microsegmentation and AI enhance cybersecurity by stopping lateral movement and reducing risks in cloud and on-prem environments.
Read MoreNotepad++ Vulnerability Exploited in Supply Chain Attack
Weekly cybersecurity newsletter covering exploited zero-days, ransomware, supply‑chain attacks, and urgent patches.
Read MoreHow to Integrate The Security Bulldog into Your Cybersecurity Jira Tickets
Step-by-step guide to connect The Security Bulldog to Jira, automate threat ticket creation, map severities, and sync real-time security alerts.
Read More