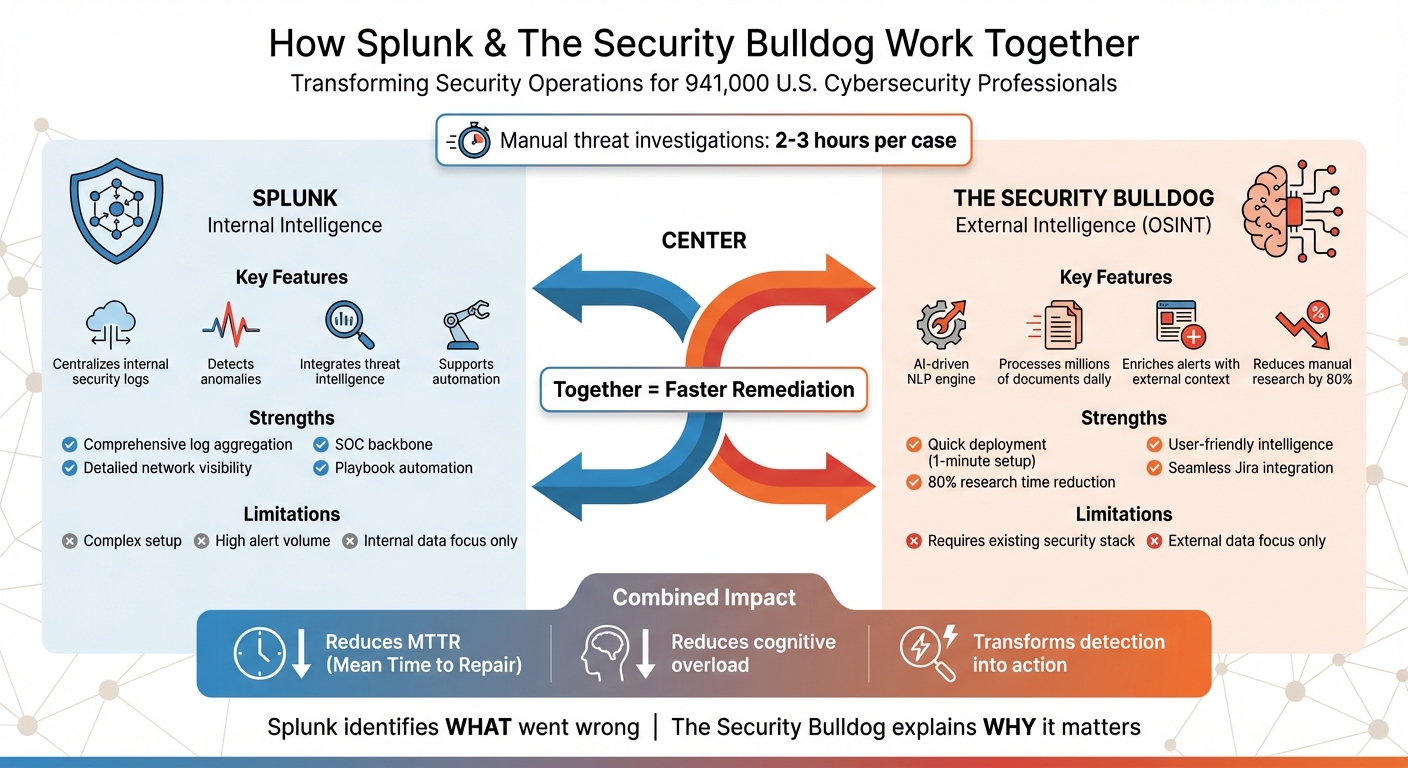
How Spunk and The Security Bulldog Work Together
Security teams are overwhelmed. With 941,000 cybersecurity professionals in the U.S. facing an avalanche of alerts and data, manual threat investigations can take 2-3 hours per case. This is where Splunk and The Security Bulldog collaborate to streamline processes and save time.
- Splunk: A powerful SIEM tool that centralizes and analyzes internal security logs, detects anomalies, and integrates threat intelligence.
- The Security Bulldog: An AI-driven OSINT platform that enriches Splunk alerts with external intelligence, providing actionable insights and reducing manual research by 80%.
Together, they transform detection into faster remediation, cutting Mean Time to Repair (MTTR) and reducing cognitive overload. Splunk identifies internal issues, while The Security Bulldog adds external context, ensuring security teams can act decisively.
| Platform | Strengths | Limitations |
|---|---|---|
| Splunk | Centralizes internal logs, offers detailed visibility, supports automation | Complex setup, high alert volume, focuses on internal data |
| The Security Bulldog | Processes OSINT efficiently, slashes research time, integrates with tools | Requires existing security stack, focuses on external data |
This partnership enables a faster, more effective response to evolving threats. Security teams can now focus on solving problems instead of being buried in alerts.
Splunk vs The Security Bulldog: Platform Comparison for Security Teams
Getting Started with Splunk Threat Intelligence 2025
1. Splunk
This section outlines Splunk’s primary features that form the backbone of its collaboration with The Security Bulldog.
Log Ingestion and Analysis
Splunk simplifies how security logs are managed by centralizing them into a single pipeline. This process covers everything from collection and ingestion to parsing, indexing, and querying, ultimately delivering insights that security teams can act on.
Its architecture relies on several key components:
- Universal Forwarders: Gather large volumes of data.
- Heavy Forwarders: Pre-process and filter out unnecessary noise.
- Indexers: Store and index data in real time.
- Search Heads: Power dashboards and configure alerts.
Security professionals use Splunk’s Search Processing Language (SPL) to filter, analyze, and perform statistical operations on indexed data. This helps uncover patterns such as brute force login attempts or unauthorized access. For instance, by correlating parent-child process IDs, teams can detect malicious execution chains, or they can identify suspicious network spikes tied to specific user activities.
Threat Intelligence Capabilities
Splunk’s Threat Intelligence Management (TIM) consolidates and enhances data from various sources like open-source feeds and malware analysis tools. By normalizing this data, the platform assigns risk scores that help analysts focus on high-priority threats.
In January 2025, Splunk introduced live integrations with Cisco Talos threat intelligence across its security tools, including Enterprise Security, SOAR, and Attack Analyzer. Cisco Talos processes an astounding 800 billion security events daily, evaluates around 2,000 new samples every minute, and uncovers 200 vulnerabilities annually. These integrations are available at no extra cost for Splunk Security cloud users.
"Threat Intelligence Management provides SOC analysts actionable intelligence with associated normalized risk scores and the necessary context from intelligence sources that are required in order to detect, prioritize and investigate security events." – Olivia Henderson, Product Marketing Lead for Splunk Enterprise Security
Alongside its intelligence capabilities, Splunk integrates easily with external systems to enable automated workflows.
Integration and Workflow Automation
Splunk enhances threat enrichment by connecting with third-party tools via SOAR connectors and Adaptive Response Actions. When used within Splunk Enterprise Security, these tools automatically add intelligence – like threat levels, categories, and reputation data for IPs, URLs, and domains – to findings.
In May 2025, Splunk’s Threat Research Team worked with Cisco’s Talos team to incorporate Firepower Threat Defense (FTD) telemetry into Splunk. Over a 60-day experiment in an AWS VPC lab, they analyzed 650,000 events across four event types and developed 17 specific detections. These included "Cisco Secure Firewall – Bits Network Activity" and "Binary File Type Download" detections. This integration allowed security teams to monitor threats across entire firewall systems rather than isolated devices.
"By integrating Cisco’s Firepower Threat Defense (FTD) with Splunk’s analytics platform, your security team immediately gains comprehensive, organization-wide visibility into network threats far beyond what any single firewall can detect alone." – Jose Enrique Hernandez, Director of Threat Research, Splunk
2. The Security Bulldog
This section explores how The Security Bulldog’s AI-powered intelligence enhances Splunk’s data processing capabilities.
Threat Intelligence Capabilities
The Security Bulldog tackles a major challenge for cybersecurity teams: managing massive data volumes. Its advanced Natural Language Processing (NLP) engine processes millions of documents daily, turning Open Source Intelligence (OSINT) into actionable insights.
Instead of simply adding more data streams, the platform focuses on delivering better answers. Using its NLP engine, it builds a curated OSINT knowledge base tailored specifically to your industry and IT environment. This includes information from sources like the MITRE ATT&CK framework, CVE databases, podcasts, and news outlets, all normalized and scored for relevance.
"We don’t need more data and alerts: we need better answers." – The Security Bulldog
By assigning risk scores, the platform helps contextualize threats and guides immediate remediation efforts. This refined intelligence bridges the gap left by raw data processing, working hand-in-hand with Splunk’s anomaly detection to provide deeper insights.
With these strong threat intelligence features, the platform seamlessly integrates into automated workflows to speed up response times.
Integration and Workflow Automation
Once the data is enriched, The Security Bulldog automates critical workflows to simplify threat response. It integrates directly with Jira ticketing systems, embedding threat intelligence into Jira tickets. This automation eliminates the typical two-to-three-hour morning threat research routine, allowing for faster remediation.
Users can set up custom feeds to filter intelligence based on their specific technology stack and threat landscape. The platform offers a quick one-minute setup and a cancel-anytime free trial. This integration ensures that when Splunk detects an anomaly or generates an alert, The Security Bulldog provides the external intelligence context needed to assess its impact and prioritize responses.
"Our proprietary natural language processing engine processes and presents the data they need in a human friendly way to reduce cognitive burden, improve decision making, and quicken remediation." – The Security Bulldog
The platform also supports real-time vulnerability mapping and anomaly detection. When combined with Splunk’s analytical tools, this pairing enhances threat prediction and transforms detection into swift, effective remediation.
sbb-itb-9b7603c
Pros and Cons
Let’s break down the strengths and limitations of Splunk and The Security Bulldog to understand how they complement each other.
Splunk serves as a powerful hub for internal data and alerts, offering unmatched visibility across your network. However, its extensive internal alerting can overwhelm security teams. On the other hand, The Security Bulldog shines in cutting through information overload with its NLP engine, which processes millions of documents daily, reducing manual research time by an impressive 80%.
| Platform | Strengths | Limitations |
|---|---|---|
| Splunk | Aggregates internal logs comprehensively; serves as the backbone of a SOC; supports orchestration and playbook automation | Complex setup; generates a high volume of alerts; focuses primarily on internal data |
| The Security Bulldog | Quick to deploy; slashes research time by 80%; provides user-friendly OSINT intelligence; integrates seamlessly with ticketing systems | Needs an existing security stack for full effectiveness; concentrates on external intelligence |
When used together, these platforms create a powerful synergy. Splunk pinpoints internal issues – what went wrong within your environment – while The Security Bulldog adds critical context, explaining why those issues matter and offering actionable remediation steps using curated external intelligence.
This integration transforms detection into faster, more decisive action. It gives security teams the tools to manage threats effectively, combining internal visibility with external insights for a comprehensive approach to threat intelligence and remediation.
Conclusion
In the U.S., around 941,000 cybersecurity professionals face the challenge of managing overwhelming amounts of data, leaving them bogged down by alerts and time-consuming manual research tasks. By combining internal telemetry with enriched OSINT, this integration streamlines security workflows and speeds up threat response. Splunk focuses on managing internal telemetry and orchestration, while The Security Bulldog automates the collection and analysis of external intelligence.
When used together, these platforms deliver clear operational benefits. The Security Bulldog significantly cuts down on the time spent on manual research, while Splunk’s SOC Operations dashboard measures the improvements in Mean Time to Triage (MTTT) and Mean Time to Remediation (MTTR). Splunk identifies internal security issues, and The Security Bulldog provides the context and solutions to address them.
To make the most of this integration, teams looking to enhance their threat intelligence and automation capabilities should leverage The Security Bulldog for automating the initial research phase of Splunk notable events. Its curated intelligence can be fed directly into Splunk investigations or Jira tickets, helping to clear backlogs more efficiently. Use Splunk’s SOC metrics dashboard to track these efficiency gains. This automated workflow replaces manual OSINT gathering, delivering faster, more actionable insights and empowering teams to act with confidence.
FAQs
What data does Splunk send to The Security Bulldog for enrichment?
Splunk integrates data such as IP addresses, threat reports, and contextual information using Spur‘s feeds and APIs to enhance its capabilities. This process includes leveraging indicators like IoCs (Indicators of Compromise) and threat intelligence to refine threat detection and analysis.
How is The Security Bulldog’s risk scoring different from Splunk’s internal scoring?
The Security Bulldog’s risk scoring leverages AI to evaluate real-time data, the likelihood of exploitation, and the importance of assets. This ensures vulnerabilities are prioritized in a way that aligns with actual risks. On the other hand, Splunk’s internal scoring often depends on static, rule-based, or signature-based methods. By using AI, Security Bulldog offers a more precise and efficient approach, simplifying decision-making for security teams.
What’s the quickest way to embed The Security Bulldog intel into Splunk or Jira workflows?
To seamlessly integrate The Security Bulldog intelligence into Splunk or Jira workflows, you can leverage API connections, automation tools, or pre-built connectors.
For Jira, set up the Splunk Add-on for Jira Cloud to automate the creation of tickets based on threat insights. This ensures that critical issues are flagged and tracked without manual intervention.
In Splunk, you can pull in The Security Bulldog’s data feeds using native automation tools like SOAR or by employing custom scripts. This helps enhance dashboards and streamline alert workflows, making threat management more efficient.